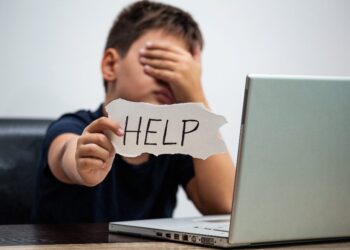
The internet, once envisioned as a borderless realm of free information and connection, has become a hotbed of transnational crime. From ransomware attacks that cripple hospitals and critical infrastructure to sophisticated scams that steal billions from individuals and businesses, cybercrime is a global pandemic that respects no national boundaries. This borderless nature of the threat has exposed a critical weakness in the international legal system, which is fundamentally designed for a world of physical borders and national sovereignty. A scammer in one country can defraud a victim in another, leaving law enforcement agencies trapped in a jurisdictional nightmare.
The urgency of this crisis has triggered a new era of legal and diplomatic efforts, aimed at forging global cybercrime treaties that can provide a unified framework for combating this threat. While the foundational legal instruments, such as the Budapest Convention, have laid important groundwork, they are now being challenged by the speed of technological change and the growing geopolitical divisions between nations. The current negotiations for a new United Nations treaty on cybercrime are a high-stakes legal battlefront that will not only redefine the rules of digital security but will also determine the balance between law enforcement, national sovereignty, and individual rights. This article will provide a comprehensive guide to the challenges of prosecuting cybercrime, the existing legal frameworks, the key points of contention in the new UN treaty negotiations, and the profound implications of these treaties for businesses, individuals, and the future of the internet.
The Jurisdictional Nightmare
The legal and law enforcement response to cybercrime is hindered by a number of systemic problems that traditional criminal law is not equipped to handle.
- Jurisdictional Conflicts: When a cybercriminal in Russia hacks a company in the United States and steals data that is stored on a server in Ireland, which country has jurisdiction? The victim’s location, the criminal’s location, and the data’s location are often in different countries with different laws. This creates a legal and logistical mess that makes prosecution incredibly difficult.
- The Challenge of Evidence Gathering: Traditional methods of evidence gathering, such as search warrants, are limited by national borders. Law enforcement agencies often need to request data and evidence from tech companies and internet service providers (ISPs) that are located in other countries, a process that can be slow and cumbersome.
- Anonymity and Attribution: The internet’s design provides a degree of anonymity that criminals exploit to mask their identities and locations. Tracing a cyberattack back to its source requires a complex process of digital forensics and international cooperation, which is often difficult to achieve.
- Lack of Universal Legal Definitions: What constitutes a “cybercrime”? While some acts, like hacking and malware, are universally illegal, others are not. A lack of standardized legal definitions of cybercrime across different countries makes it difficult to prosecute criminals and to share evidence and intelligence.
The Foundational Framework
For over two decades, the Budapest Convention on Cybercrime has been the world’s most influential and widely adopted cybercrime treaty. It was a landmark legal instrument that established a framework for international cooperation and harmonized national laws.
- Key Provisions: The Convention requires member states to criminalize a range of offenses, including illegal access, data and system interference, and computer-related fraud. It also established a framework for international cooperation, including mechanisms for mutual legal assistance, extradition, and the preservation of digital data.
- Successes and Limitations: The Convention was a groundbreaking achievement that has been instrumental in numerous cross-border cybercrime investigations. However, its effectiveness is limited by a number of factors. It has not been universally adopted, with major countries like Russia and China choosing not to ratify it. Its provisions, written in 2001, are also struggling to keep up with the pace of technological change and the evolution of cybercrime. The rise of new crimes, such as ransomware and AI-driven deepfake fraud, was not foreseen by the Convention, creating a legal gap.
The New UN Treaty

Recognizing the limitations of the Budapest Convention, the United Nations has embarked on a new, high-stakes negotiation for a comprehensive global cybercrime treaty. This process has become a major legal and geopolitical battlefront, with countries deeply divided over its scope and purpose.
A. The Scope and Definition of Cybercrime:
A key point of contention is what, exactly, the treaty should cover.
- The U.S. and European View: Developed nations, led by the U.S. and the EU, argue that the treaty should focus on traditional “high-tech” crimes, such as hacking, malware, and financial fraud. They fear that a broader definition would be used by authoritarian regimes to criminalize political dissent and restrict freedom of speech online.
- The Russian and Chinese View: Countries like Russia and China argue for a much broader definition of cybercrime, which would include offenses such as the dissemination of “untrue” information, online hate speech, and even what they consider “unlawful content.” Critics fear that this broad definition would be used as a tool for political repression and censorship.
B. Human Rights, Privacy, and Surveillance:
The treaty negotiations are a clash between law enforcement’s need for data and an individual’s right to privacy and human rights.
- Access to Data and Encryption: Law enforcement agencies are pushing for provisions that would require tech companies and internet service providers to provide them with access to user data. This has led to a fierce debate over encryption. Privacy advocates and tech companies argue that requiring a “backdoor” to encryption would weaken security for all users and make them more vulnerable to hackers and state-sponsored attacks.
- Due Process and Judicial Oversight: Human rights organizations are pushing for strong due process protections in the treaty, ensuring that law enforcement access to data is subject to judicial oversight and that a person’s digital rights are protected.
C. Sovereignty and Jurisdiction:
The treaty negotiations are also a debate over national sovereignty and who has the right to prosecute a cybercriminal.
- Cross-Border Investigations: Developed nations are pushing for new mechanisms that would allow for faster and more efficient cross-border investigations. This includes provisions for a country to collect data from a company located in another country without going through a lengthy mutual legal assistance treaty process.
- Digital Sovereignty: Some countries, particularly those with more authoritarian governments, fear that these provisions would be used to undermine their national sovereignty and to interfere with their internal affairs. They are pushing for language that would protect their right to control data and digital infrastructure within their own borders.
D. The North-South Divide:
The treaty negotiations have exposed a significant divide between developed and developing nations.
- Capacity Building: Developing nations argue that they lack the resources, expertise, and legal frameworks to effectively combat cybercrime. They are pushing for provisions in the treaty that would require developed nations to provide them with funding, training, and technology to build their capacity to fight cybercrime.
- Differing Priorities: Developed nations are often focused on financial fraud and ransomware attacks, while developing nations may have a different set of priorities, such as protecting critical infrastructure or combating cyber-enabled human trafficking.
The Impact on Businesses and Individuals
The outcome of these treaties will have a profound and lasting impact on businesses, individuals, and the future of the internet.
- For Businesses: A new treaty could create a unified set of legal rules for cross-border data transfers and cybercrime investigations, which would simplify compliance and reduce legal costs. However, it could also impose new requirements for data retention and security, and create a new risk for companies that operate in countries with different legal systems.
- For Individuals: The treaties could provide new legal protections for victims of cybercrime, making it easier to seek justice and recover stolen funds. However, they could also be used to justify mass surveillance, to criminalize freedom of speech, and to undermine individual privacy rights.
Challenges and the Path Forward
The path to a successful global cybercrime treaty is fraught with challenges, but the urgency of the threat demands that a solution be found.
- Geopolitical Tensions: The ongoing geopolitical tensions between major powers, particularly the U.S. and Russia, are a major hurdle to finding a common ground. The negotiations are often seen as a proxy war for control of the digital realm.
- The Speed of Technology: The legal process is inherently slow, while technology is evolving at a breakneck pace. By the time a treaty is ratified, it may already be outdated.
- Public-Private Partnerships: The solution will likely require a new model of cooperation. Law enforcement and governments must work more closely with the private sector, which has the technical expertise and the data to track and combat cybercrime.
Conclusion
The negotiations for a new global cybercrime treaty are a defining moment in the history of the internet. They are a necessary and vital response to a threat that has grown too large for any one nation to handle. The battle is complex, touching on a host of fundamental legal and ethical issues, but its outcome will determine the future of digital security and individual freedom. The old legal frameworks are obsolete, and new ones are being forged in real-time.
The most successful outcome would be a treaty that provides a unified framework for international cooperation, one that focuses on serious, high-impact cybercrimes, while also enshrining and protecting human rights. It would be a treaty that empowers law enforcement without enabling surveillance, and one that provides new tools for justice without undermining a citizen’s right to privacy. The future of a secure, open, and free internet depends on our ability to navigate this legal and diplomatic battlefield with foresight, wisdom, and a commitment to justice. The legal foundations we build today will determine the level of security we can expect in the digital world for generations to come.










Discussion about this post